When your EDR alerts on suspicious activity, how do you know it caught everything?
Endpoint triage is the step SOC teams use to verify nothing was missed. After reviewing the EDR alert, they investigate the actual endpoint to find evidence the EDR didn’t detect.
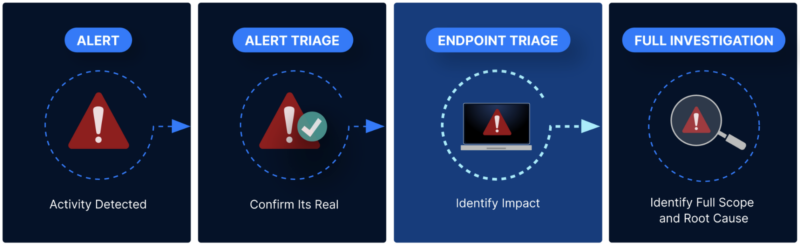
Think of it like this: The EDR is your burglar alarm. It detected an intrusion. Endpoint triage is checking if the burglar left tools behind, propped open a back door, or is still hiding in the basement.
But here’s the challenge: manual endpoint triage takes 60 to 90 minutes per alert. For SOCs handling 50+ alerts per day, that’s not scalable.
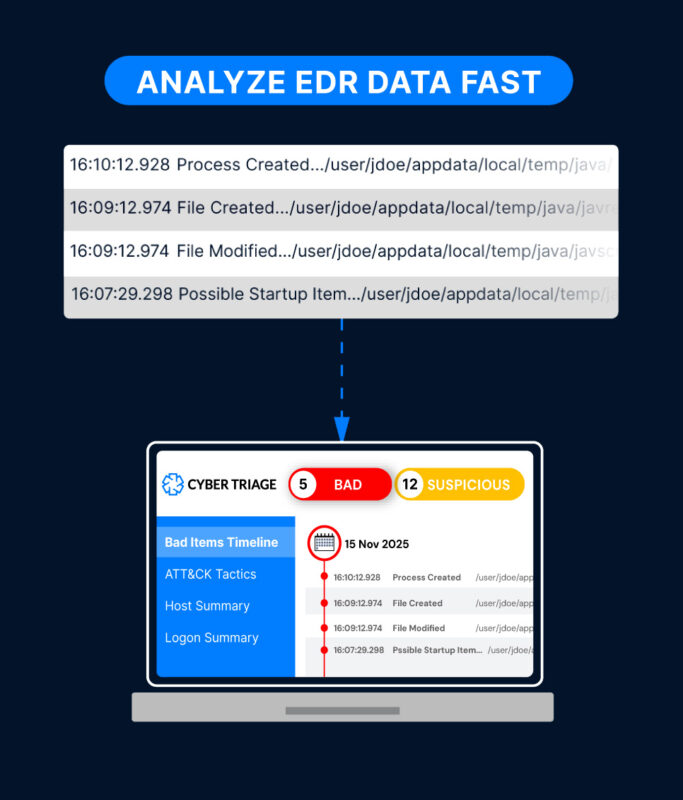
Quickly Find Evidence with Automated Scoring
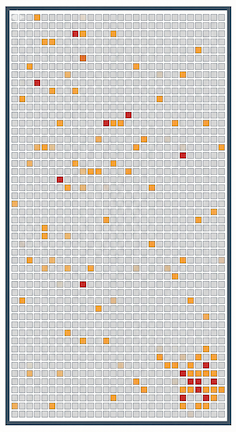
The most time consuming part of any investigation is finding evidence because it is not common and attackers try to blend in.
The way to quickly find it is using automated analysis to score items as bad, suspicious, or good. Investigators should focus on the bad and suspicious.
If analysts manually review EDR telemetry or forensic collections, the process takes too long and is often prematurely stopped because the clock has run out.
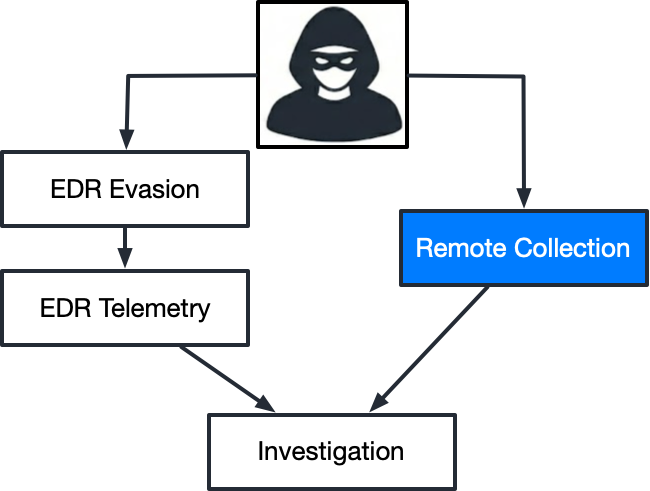
Automatically Extend Your Telemetry
Nearly all attackers are now using EDR evasion to bypass detection. Some of these techniques mean that your EDR telemetry does not have evidence of the attack.
To make sure you see evidence of the attacker when they use EDR evasion, go to the endpoint to collect additional data.
This can be done automatically using SOAR platforms, forensic collectors, and existing EDR agents (many allow you to run 3rd party collectors).
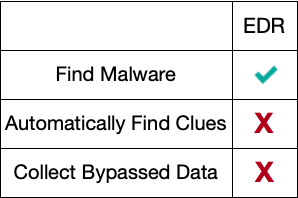
Why EDRs aren’t Enough
EDRs are not sufficient for endpoint triage because:
- No Suspicious Scoring: EDRs contain massive amounts of data that must be manually reviewed. They do not have automated scoring to identify the suspicious stealthy activity that attackers use to blend in.
- Incomplete Data: If EDR evasion was used, the EDR does not contain evidence of the attack. A 2nd opinion is needed.
SOCs need an automated investigation platform that builds on top of the EDR. It uses the EDR telemetry, gets additional data, and scores it.
Getting Started with Endpoint Triage
If your SOC isn’t doing endpoint triage today, start with high priority alerts:
- Alerts involving privileged accounts
- Alerts on critical systems (domain controllers, file servers)
- Alerts with lateral movement indicators
- Any alert where the timeline seems incomplete
Use an investigation platform to automate the collection and scoring. Manual endpoint triage is too slow for daily SOC operations.
How Cyber Triage Helps
Cyber Triage automates endpoint triage for SOC teams:
- Deploys collectors to endpoints in seconds
- Collects forensic data the EDR doesn’t capture
- Scores artifacts using malware scanning, behavioral analysis, and threat intelligence
- Shows analysts exactly what to investigate first
SOC teams use Cyber Triage alongside their EDR to ensure nothing gets missed when closing alerts.