In our recent survey of SOC managers, over 70% admitted they often or always worry about persistent threats after alerts are closed.
There are three causes:
- Too much telemetry data
- Not enough time
- Stealthy and evasive attackers
The result is concern that the analyst missed something that happened days before an alert.
Investigation Challenges
1. Telemetry Overload
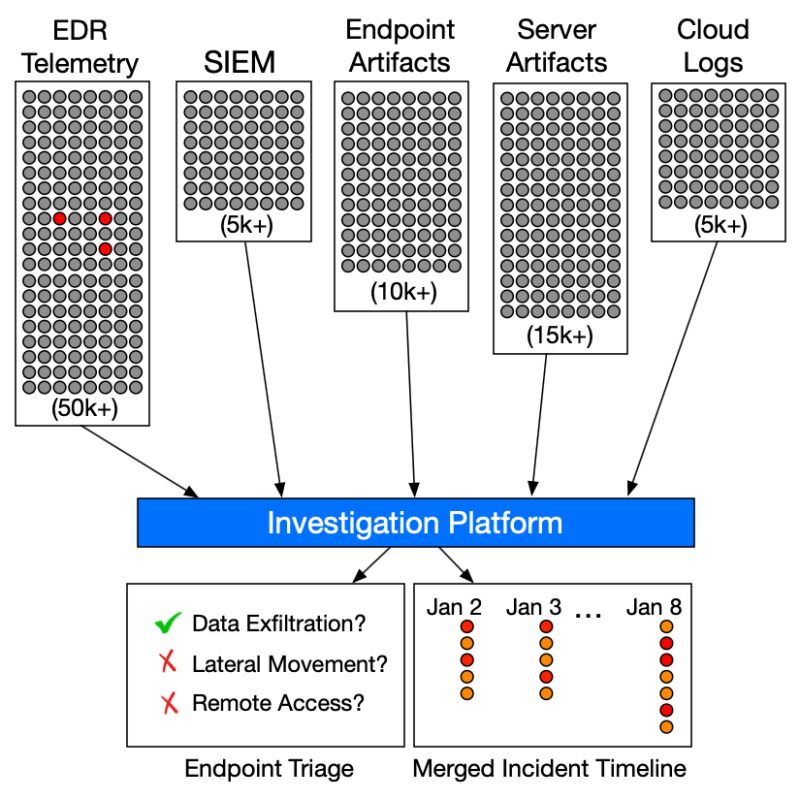
To look for data exfiltration, remote access, and persistence, analysts need to review 50k+ events in the EDR. It’s overwhelming, especially for Jr Analysts.
99.9% of the EDR telemetry is boring. It’s hard to find the 0.1% that is relevant using manual techniques.
Solution: Use automated analysis. EDRs won’t flag suspicious activity, but you can export the data to an investigation tool that will.
2. Time Constraints
Many SOCs have time constraints per alert to make sure the backlog does not get too large.
This forces analysts to close investigations before fully exploring lateral movement or data exfiltration. Given another 15 minutes, they might have found something.
Solution: Automate as much as possible to increase velocity and give more time based on type of alert and asset.
3. EDR Evasion
Every threat actor has a preferred EDR evasion technique. They disable agents, operate in memory, or use living-off-the-land (LOLBin) tactics that don’t trigger alerts.
If an analyst relies solely on EDR telemetry, they’re investigating with incomplete data. Critical evidence may simply not exist in the EDR logs.
Solution: Deploy a forensic collector to collect artifacts that may show activity that the EDR missed.
Automate Your Investigations
Investigation platforms address these concerns by:
- Automatically score data so that relevant data is highlighted
- Quickly analyzing and enriching data within the allowed time
- Collect additional data (in case of evasion)
This ensures junior analysts don’t miss critical evidence, provides a second opinion when EDR has gaps, and dramatically speeds up investigations.
How Cyber Triage Helps
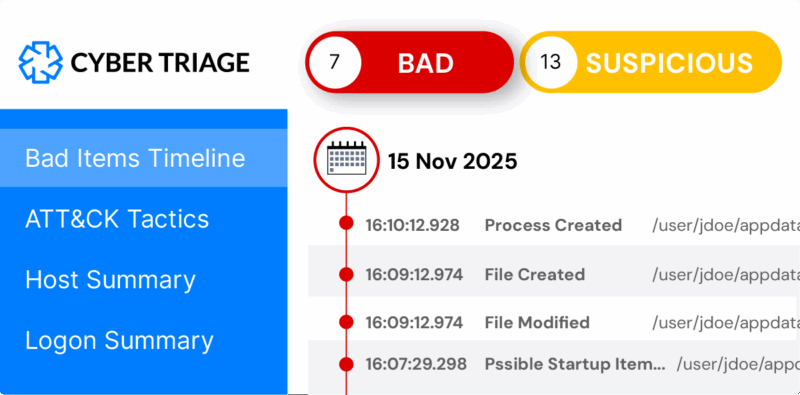
Cyber Triage imports your EDR telemetry and deploys its own collector for a complete picture. It automatically scores artifacts and shows what’s bad, suspicious, or safe.
SOC teams using Cyber Triage close alerts faster and with more confidence.
