Rapidly Investigate Cyber Incidents
Automated Investigation Platform for SOCs, MSSPs, DFIR Teams, and Law Enforcement
Cyber Triage is automated DFIR software that empowers your team to quickly investigate incidents.
Host-based data, scoring, advanced analytics, and a recommendation engine ensure your investigations are fast and comprehensive.
Trusted by
Investigate Beyond Your EDR
EDRs are for detection. Not investigation.
Cyber Triage allows SOC analysts to find evidence EDRs miss:
- Access data hidden by EDR evasion or past retention dates.
- Review artifacts around the alert to identify undetected activity.
- Get clues of suspicious activity the EDR didn’t flag.
Endpoint triage shows you the impact of the alert.
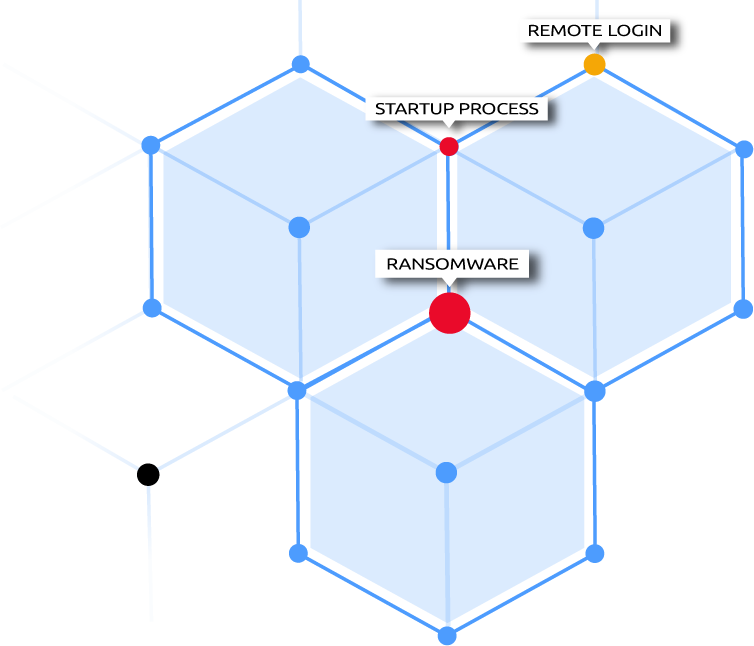
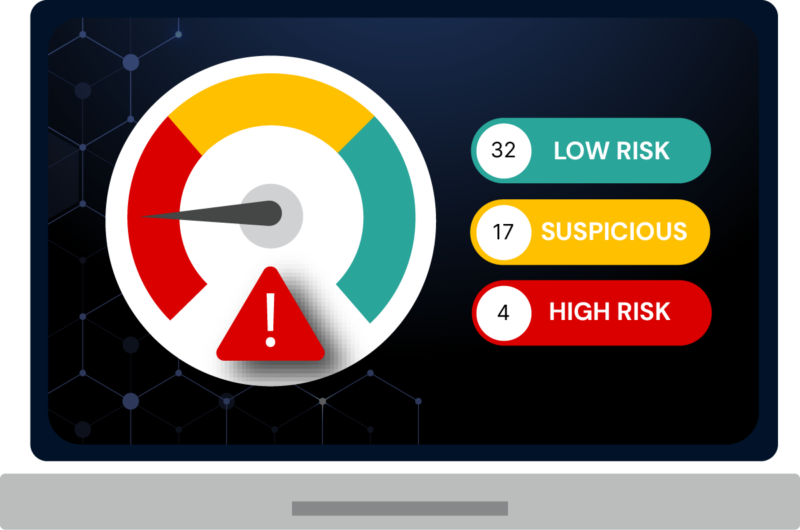
The Leader in Automated Analysis
Cyber Triage is the only SOC DFIR tool that will:
- Score artifacts so you quickly focus on relevant data.
- Scan executables with 40+ malware detection engines.
- Deploy in environments agents can’t be used.
- Recommend artifacts so you follow up on all leads.
SOCs, MSSPs, consultants, and law enforcement all use Cyber Triage to answer hard investigative questions like “What did the attacker do?” or “How did they get in?”
Complete Your Investigations Faster
Get evidence before it’s gone and minimize attack damage.
Cyber Triage maximizes speed by:
- Identifying relevant artifacts and showing them first.
- Recommending artifacts so you quickly follow all leads.
- Integrating with EDRs and SOARs so collections start ASAP.
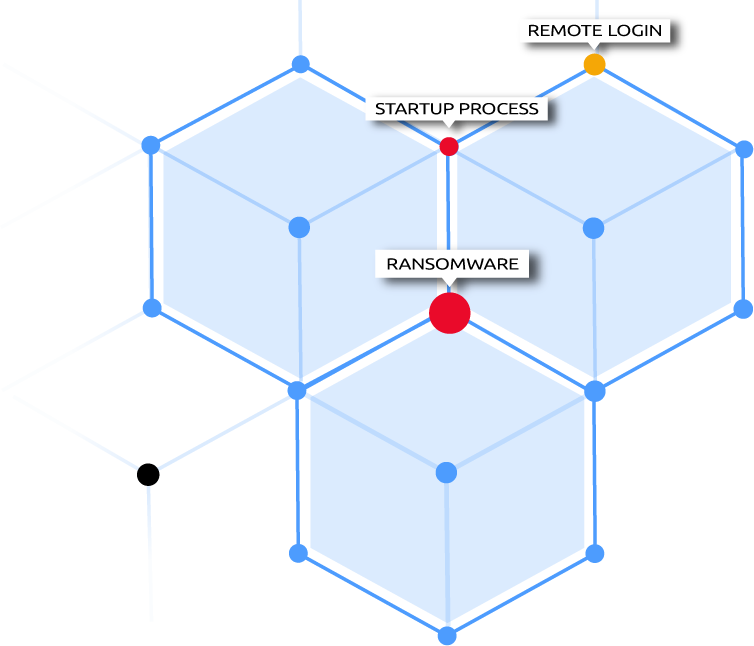
Conduct More Comprehensive Investigations
Fully understand scope and remove persistence mechanisms.
Cyber Triage gives you breadth by:
- Collecting dozens of artifact types based on numerous attack scenarios.
- Analyzing executables with 40+ malware engines.
- Using threat intel to update collection methods and heuristics.
Flexible Deployments
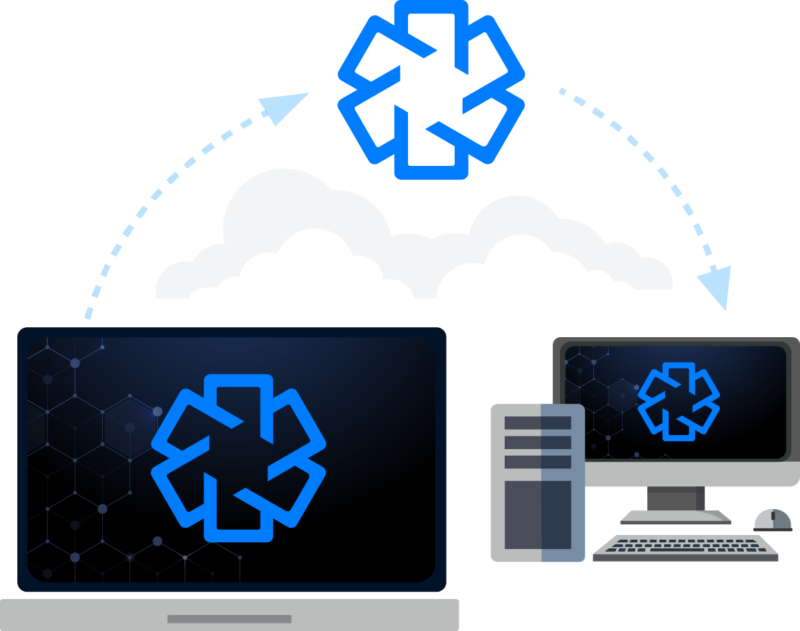
Investigations using Cyber Triage have these steps:
- Agentless collection tool collects data and sends artifacts over the network, to USB, or S3.
- Artifacts are analyzed and scored using threat intel
- Correlations are made between hosts.
- Responders review artifacts and dive deeper based on the questions they need answered.
- Additional hosts are collected from and added to the incident.
Cyber Triage is designed to work in any scenario a Cyber First Responder finds themselves in. It can run on a laptop, the cloud, or an on-premise server.
Learn DFIR Free with Brian Carrier
Intrusion investigations are amongst the most difficult for digital forensic investigators because there are so many types of evidence to look for. Our Divide and Conquer DFIR Process helps investigators answer these hard questions by breaking them into smaller questions.
Built by Forensics Veterans
Cyber Triage is built by Sleuth Kit Labs, a spinout of BasisTech. This is the same team responsible for 20+ years of open source tools, including Autopsy and The Sleuth Kit (TSK). Sleuth Kit Labs believes in making the jobs of those on the front lines easier by making software that is automated and easy to use. The company understands that it can’t decrease first responders’ responsibilities, but it can make digital forensics as easy and effective as possible.

Get Cyber Triage
Try Cyber Triage to see how it will make your intrusion investigations faster and more comprehensive. Fill out this form to get an installer. Get started with our scenario data (or your own).
Download your free 7-day evaluation
with scenario data