Everyone is looking at Exchange Servers after Volexity observed exploitation of some 0-day vulnerabilities. While working with our customers, we added some Exchange-specific features that are now part of the 2.14.4 release.
Notably:
- Ensuring that files are collected for WebShell detection
- Distributing Yara rules to detect WebShells
This blog post covers more about that. You can get the latest release from here.
Detecting WebShells (In General)
After exploitation, it was reported that the Hafnium group was installing WebShells to retain access to various systems. WebShells are scripts placed on a web server that allow a remote attacker to get shell access or execute other commands by using a specific URL.
In our Divide and Conquer DFIR approach, detection of a WebShell fits into the investigative question of “Are there suspicious startup items” because the webserver will (likely) start each time the computer starts and will automatically make the WebShell service available. It’s equivalent to a backdoor process, except that it’s running inside of the webserver process.
There are two high-level steps to detecting the WebShell:
- You need to have access to the various ASPX and other file types that are in the wwwroot folder of the server
- You need to be able to detect which files are malicious and which simply serve up normal content.
The 2nd step is obviously the harder part, like detecting most types of malware. You can detect using signatures and other dynamic techniques.
Detecting WebShells in Cyber Triage
The latest version of Cyber Triage has:
- Expanded collection to ensure we get files for IIS / Exchange servers
- Preconfigured Yara rules from the NSA Github Repo to flag web shells.
There are no additional steps to have this happen.
- Collection: Regardless of if you collect over the network, from a USB drive, or upload to S3 bucket, the agentless collection tool will collect wwwroot files if you choose to collect Startup Items
- Analysis: All collected items are analyzed and scored by Cyber Triage and the wwwroot files will get additional analysis using the Yara rules. You are free to add any other additional Yara rules that will be applied to all files.
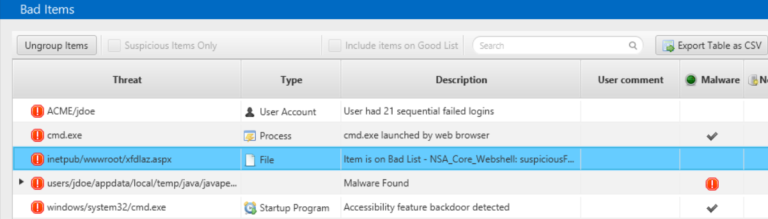
If you have a file that is flagged by the Yara rules, it will look something like this:
About Cyber Triage
Cyber Triage is automated incident response software that allows you to quickly and comprehensively investigate endpoints and servers by focusing on:
- Automated Collection to ensure thousands of artifacts are retrieved
- Scoring to ensure the examiner can focus on the small number of relevant artifacts
- Recommendation to ensure all of the investigation threads are followed.
Cyber Triage is used by MSSPs, corporations, consultants, and law enforcement around the world to save hours on their investigations.
Try It Today
You can get a free 7-day eval copy of Cyber Triage by filling out this form. You can also sign up for our webinar to see it in action and ask questions.