As a consultant, you need to quickly understand the scope of an incident, but when you don’t have easy access to a network or if it’s unfamiliar, progress can be slow.
Cyber Triage allows you to:
Collect Without Agents
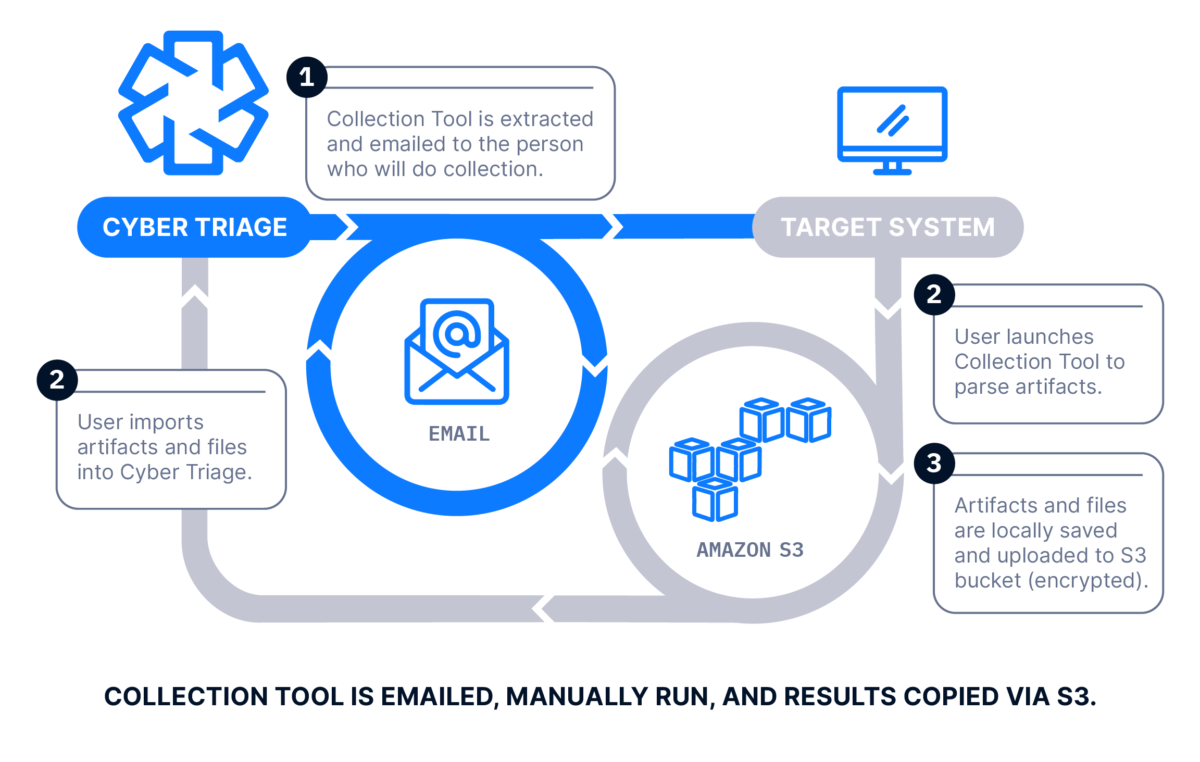
When clients don’t have endpoint visibility or telemetry data, you are forced to deploy your own solutions. Cyber Triage is an agentless system that supports many methods of collecting and importing data.
Some common methods used include:
- Emailing the collection tool to your customer for them to run and upload data to an S3 bucket.
- Adding a Cyber Triage Team Server to the client network and initiating collections over the network.
Get a Starting Point
In a new environment, it can be daunting to know where to start. Cyber Triage helps you find that starting point by:
- Collecting from many hosts at a time with no user interaction.
- Automatically analyzing and scoring the hosts to identify attacker activity.
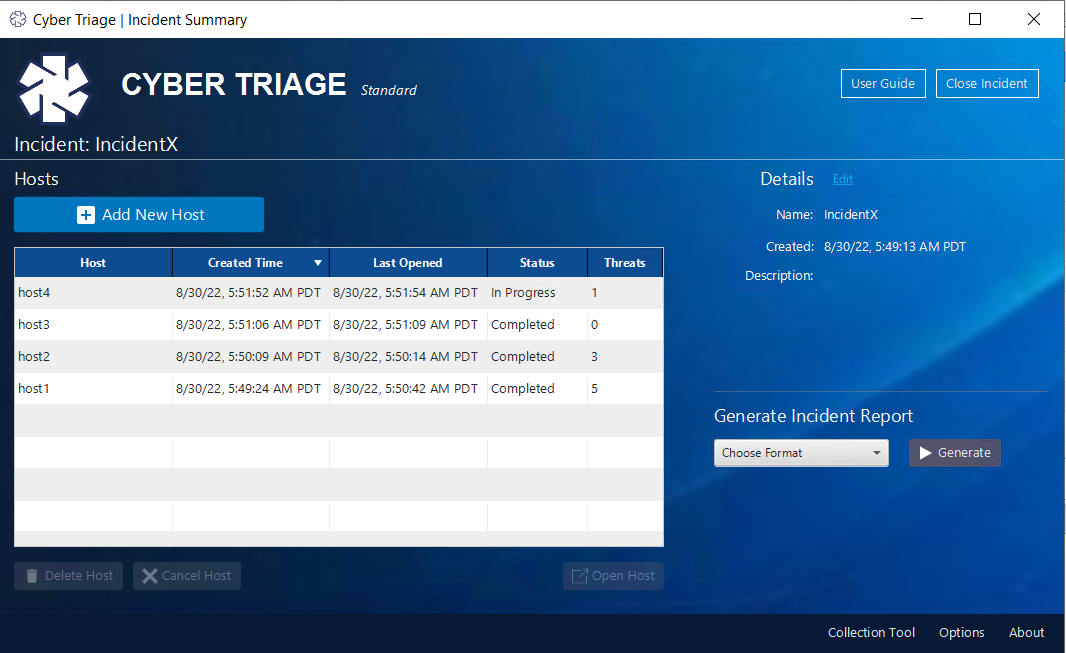
The responder can then review the Incident Dashboard to decide which host to focus on first. The results of the first host will be leveraged by later hosts.
Determine What’s Normal
When reviewing hosts in a client’s environment, it can be hard to know what processes or startup items are common or an indication of an issue. What may be normal for that environment may be unusual to you and send you down the wrong path.
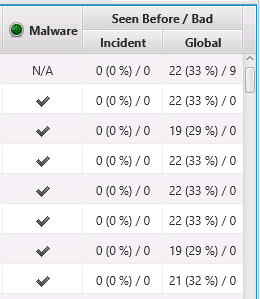
Cyber Triage will remove uncertainty by showing you:
- How common an item is within an incident
- How often an item has been seen in all of your past cases
- If it has been marked as bad in those incidents
This helps you figure out if it’s an anomaly or common.
Consultants Are Using Cyber Triage



Faster Forensics For Even Faster Remediation With Cyber Triage Digital Forensics Tool
Plans start as low as $208/month for unlimited support and 4000 daily scans with ReversingLabs.