Skip to content
Cyber Triage Lite – Identifying Malware
May 23, 2022
Start Reading
Cyber Triage 3.2.0: Batching, Streaming and KAPE
April 5, 2022
Start Reading
Cyber Triage Lite – Analyzing User Activity
March 24, 2022
Start Reading
Cyber Triage Lite – Network, Disk Image, and Memory Inputs
March 10, 2022
Start Reading
Cyber Triage Lite – Intro and USB-based Collection
February 16, 2022
Start Reading
Cyber Triage 3.1.0: Artifact Searching and OS Settings
February 10, 2022
Start Reading
General Purpose vs Specialized Digital Forensics Tools
January 24, 2022
Start Reading
Cyber Triage 3.0.2: Ransomware & Encrypted Database Detection
November 30, 2021
Start Reading
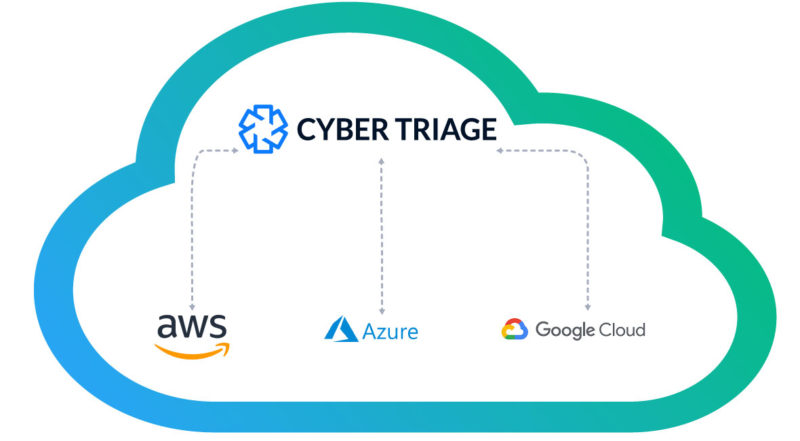
Cyber Triage on Azure: DFIR in the Cloud
November 4, 2021
Start Reading
Cyber Triage on Google Cloud: DFIR in the Cloud
October 21, 2021
Start Reading
Cyber Triage on AWS: DFIR in the Cloud
October 14, 2021
Start Reading